Beyond Classical Bits: Building a Quantum-Input Complexity Theory
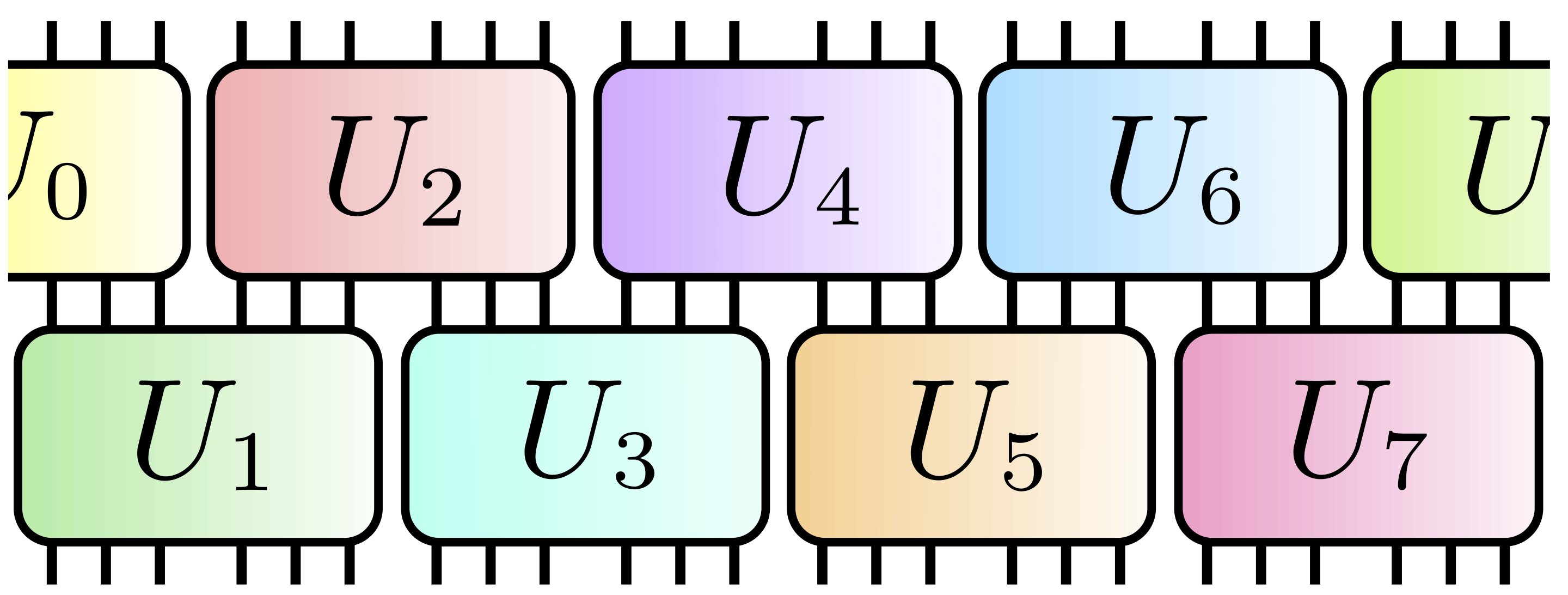
Henry Yuen is building a fully quantum complexity theory to analyze problems whose inputs and outputs are quantum, something traditional theory can’t capture. By recasting issues through the lens of Uhlmann’s theorem, his work shows several quantum-input problems—bit commitments, black-hole decoding, quantum data compression—are actually equivalent, suggesting a unified, quantum-only framework. The project seeks to map these relationships and assess whether quantum-input problems are logically independent from classical complexity, while also sharing Yuen’s personal journey and research philosophy.