
Cybersecurity News
The latest cybersecurity stories, summarized by AI
Featured Cybersecurity Stories


AI Chat Assistants Could Serve as Stealthy Malware C2 Relays
Cybersecurity researchers warn that AI assistants with web-browsing capabilities (such as Microsoft Copilot and xAI Grok) can be hijacked as stealthy, bidirectional command-and-control relays. By feeding crafted prompts, attackers can issue commands to a compromised host and exfiltrate data via trusted AI services, effectively turning living-off-trusted-sites (LOTS) into C2 channels and enabling AI-assisted malware operations and real-time evasion, without requiring API keys.

More Top Stories
Week in Cybersecurity: Proxy Botnet Disrupted, Office Zero-Day Patched, MongoDB Extortion Surges
The Hacker News•23 days ago
More Cybersecurity Stories

Global cloud-storage scam hits inboxes with fake renewal alerts to steal payment details
A worldwide phishing campaign floods recipients with urgent emails claiming cloud-storage renewals failed, pushing them to a fake Google Cloud Storage link that redirects to scam pages impersonating cloud portals. The pages upsell a deceptive “loyalty” upgrade and collect credit card info, with the aim of affiliate revenue. Legitimate providers do not notify via such scans or require third-party security products, and users should delete the messages and verify billing directly on official sites.
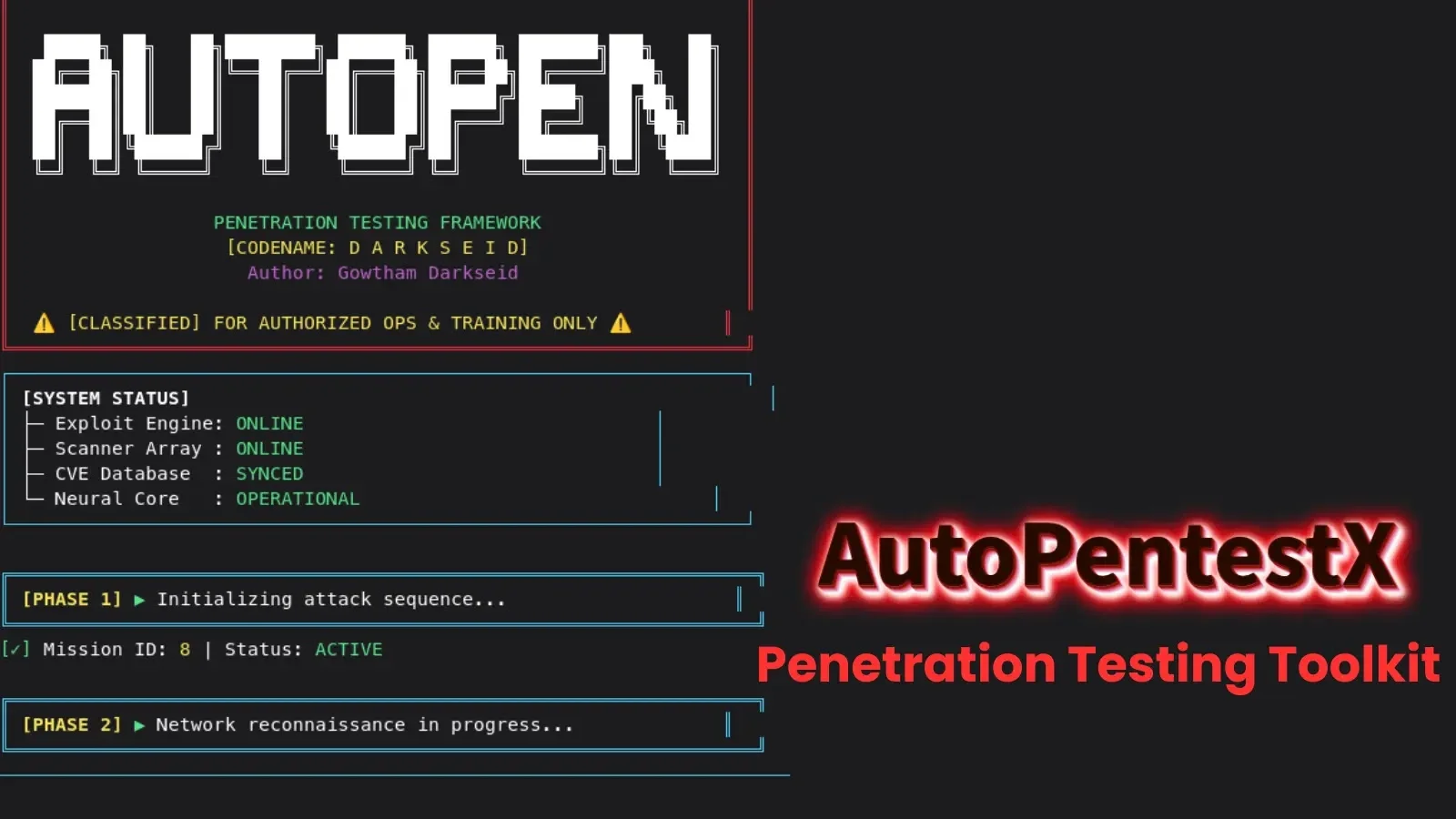
AutoPentestX: An Open-Source Linux Toolkit for Automated, Safe Penetration Testing
AutoPentestX is an open-source automated penetration testing toolkit for Linux (Kali, Ubuntu, Debian-based), released in late 2025. It automates OS detection, port scanning, service enumeration, and vulnerability checks using Nmap, Nikto, SQLMap, and Metasploit RC scripts, stores results in SQLite, and generates PDF reports with CVSS-based risk scores and remediation guidance. It supports a safe, non-destructive testing mode, is intended for authorized security assessments, and includes installation via a setup script or Python virtualenv; future plans include multi-target support and ML-assisted predictions.
Misconfigured Moltbot dashboards leak credentials and invite takeovers
Misconfigured Moltbot (formerly Clawdbot) control panels exposed hundreds of internet-facing dashboards, leaking API keys, private chats and other credentials. With autonomous agent capabilities, attackers could impersonate operators, inject messages, and even run commands with elevated privileges. The root cause was localhost-trust and reverse-proxy defaults; the project has rebranded Clawdbot to Moltbot (Molty) while keeping the same core functionality.
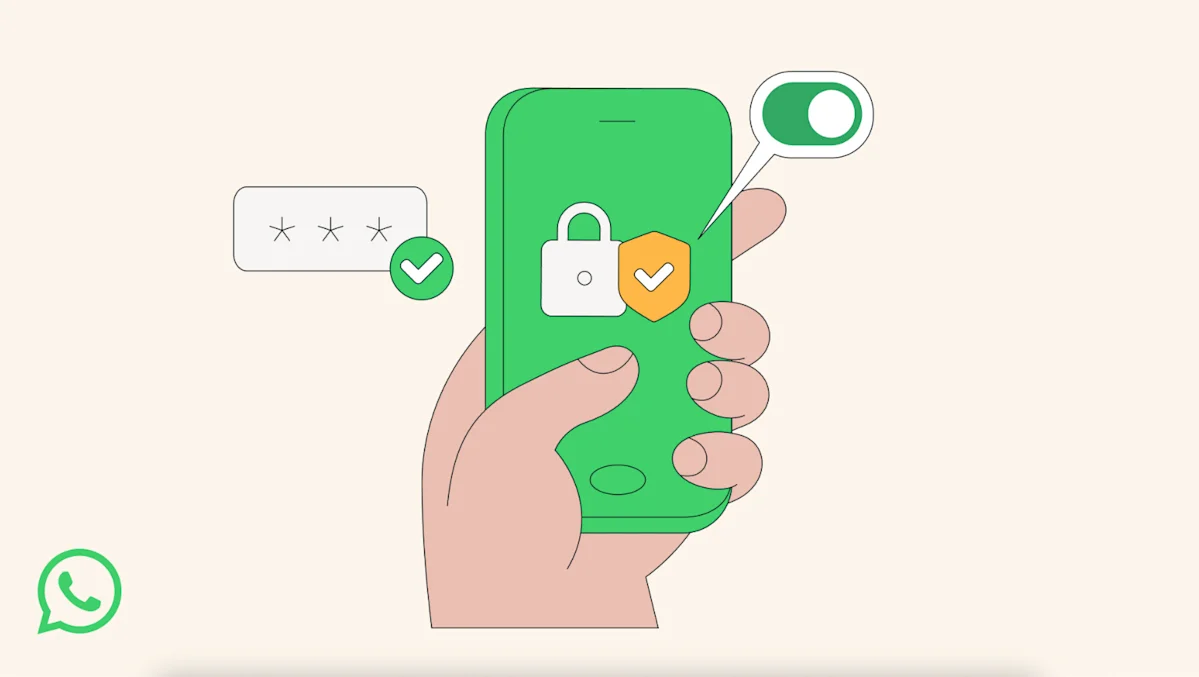
WhatsApp unveils a Tightened Privacy Mode to fend off targeted hacks
WhatsApp has introduced Strict Account Settings, a one‑click privacy feature designed for high‑risk users (such as journalists and public figures). It blocks attachments from unknown senders, disables link previews, and silences calls from unknown contacts, while regular chats remain protected by end‑to‑end encryption. The rollout will be global in the coming weeks and is aimed at providing extra safeguards against sophisticated cyberattacks.

CISA warns four enterprise flaws actively exploited across Versa, Zimbra, Vite, and Prettier
CISA has added four actively exploited vulnerabilities to its Known Exploited Vulnerabilities catalog: CVE-2025-31125 and CVE-2025-34026 affecting Versa software (including the Concerto SD-WAN) via dev-exposure and Traefik misconfig, CVE-2025-68645 in Zimbra Webmail Classic UI (local file inclusion), and a supply-chain issue in eslint-config-prettier (CVE-2025-54313) tied to Prettier. Patches or mitigations exist for affected products; US federal agencies must apply updates or stop using the products by February 12, 2026. The status of ransomware-related exploitation remains unknown.

Public Database Leak Exposes 149 Million Logins, Highlighting Infostealer Risk
A publicly accessible database exposed 149 million account credentials, including 48 million Gmail logins and 17 million Facebook logins, along with government, banking, and education accounts. The researcher who found it suspects infostealing malware collected the data, and the provider took the trove down after being alerted; the leak highlights how unsecured databases can become a goldmine for cybercriminals.
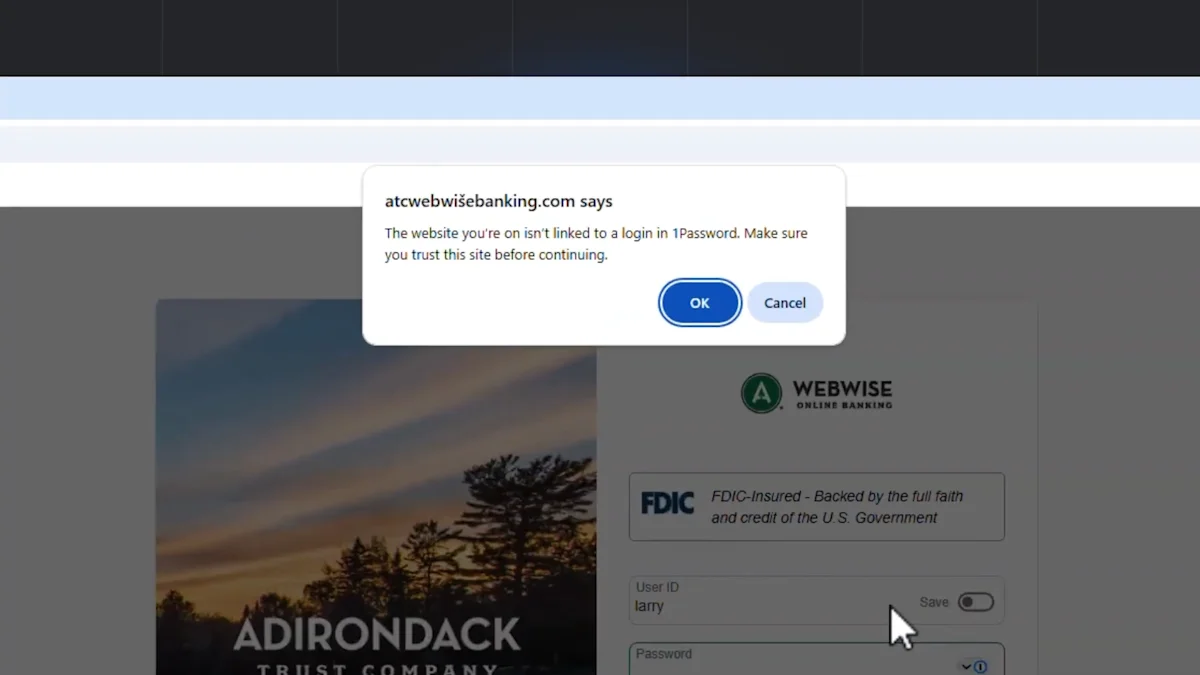
1Password adds paste-warning to curb phishing scams
1Password's browser extension now warns users if they try to paste credentials on a site not linked to their vault, adding a second layer of protection against increasingly convincing phishing scams driven by AI. The alert appears before signing in, and the feature can be enabled in the extension's Notifications settings starting today.
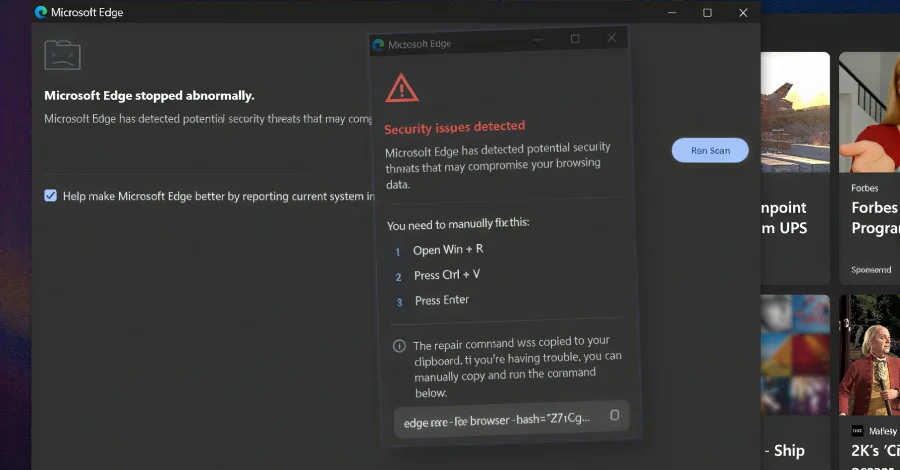
CrashFix Chrome Campaign Traps Users With DoS Crash to Deliver ModeloRAT
Security researchers detail KongTuke's CrashFix campaign, where a counterfeit Chrome extension named NexShield clones uBlock Origin Lite, issues a fake security warning, and triggers a DoS-style crash to coerce users into running a command. The attack uses a 60-minute delayed, multi-stage payload that reports a unique ID to nexsnield[.]com, fetches subsequent stages via PowerShell, and loads the ModeloRAT payload on domain-joined machines via RC4-encrypted C2 and Registry persistence; standalone hosts see a testing payload first. The operation leverages a traffic distribution system and underscores evolving social engineering and self-sustaining infection loops.

Cloudflare WAF Bypass Flaw Exposed Origins via ACME Path, Patch Deployed
Researchers disclosed a critical flaw in Cloudflare’s edge processing that allowed requests to the ACME HTTP-01 validation path (/.well-known/acme-challenge/) to bypass WAF rules and reach origin servers, potentially exposing data across common frameworks (e.g., Spring/Tomcat, Next.js, PHP). Cloudflare issued a fix on Oct 27, 2025 ensuring ACME traffic is evaluated by WAF rules again; no customer action is required and there’s no evidence of exploitation in the wild.

WhisperPair flaw lets hackers eavesdrop on select Google Fast Pair devices
Security researchers disclosed a flaw called WhisperPair in Google's Fast Pair protocol that could let an attacker within Bluetooth range pair with 17 affected headphones and speakers from 10 brands, enabling microphone access, ambient audio eavesdropping, audio injection, or location tracking. Google says Pixel Buds are patched and has provided fixes to OEMs; some updates require the manufacturer’s app. The researchers demonstrated the vulnerability and noted patches have been rolled out, though workarounds exist and continued vigilance on firmware updates is advised.
