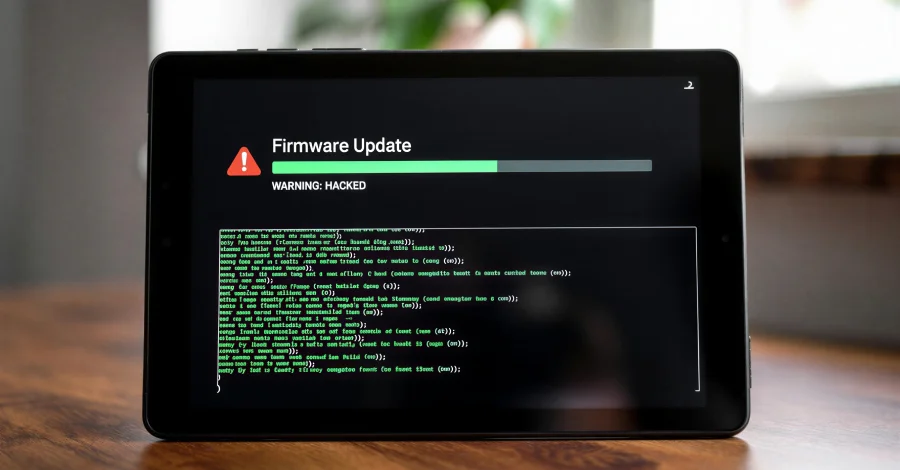
Keenadu: A firmware-level Android tablet backdoor hidden in signed OTA updates
A new Android backdoor named Keenadu is embedded in tablet firmware and distributed via signed OTA updates, enabling attackers to remotely control devices, hijack browsers, monetize app installs, and exfiltrate data through a multi-stage loader that operates across all apps. It also spreads via trojanized apps on Google Play, with Google removing three related apps and Play Protect offering protection. About 13,700 users have been affected worldwide, with clusters in Russia, Japan, Germany, Brazil, and the Netherlands. Keenadu targets core Android components (libandroid_runtime.so, Zygote, system_server) to bypass sandboxing, allowing payloads to be delivered per targeted app and enabling broad control over the device.