PromptSpy uses GenAI to persist on Android via AI-guided UI manipulation
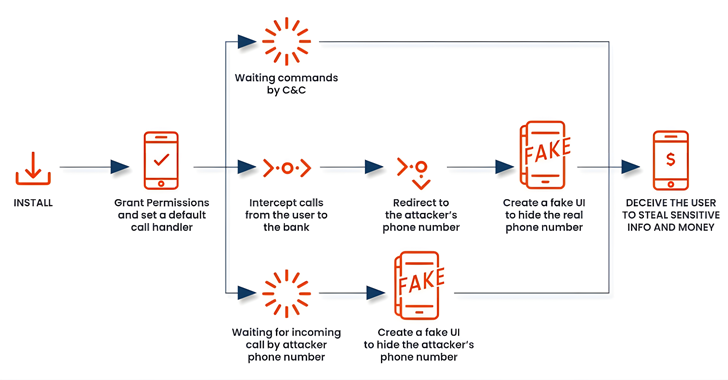
ESET researchers uncovered PromptSpy, the first known Android malware to use generative AI (Google Gemini) to drive UI-level actions for persistence. By feeding Gemini an XML snapshot of the current screen, the AI returns step-by-step tap instructions to keep the app in the recent apps list, while a built-in VNC module provides remote access. The malware also exploits Accessibility Services, overlays to hinder uninstallation, and can capture lockscreen data and screen video. Distribution appears tied to Argentina via a banking/phishing site; no Google Play presence. This example shows how AI can make Android threats more adaptive and harder to defeat.