Amaranth-Dragon weaponizes WinRAR flaw for Southeast Asian espionage campaigns
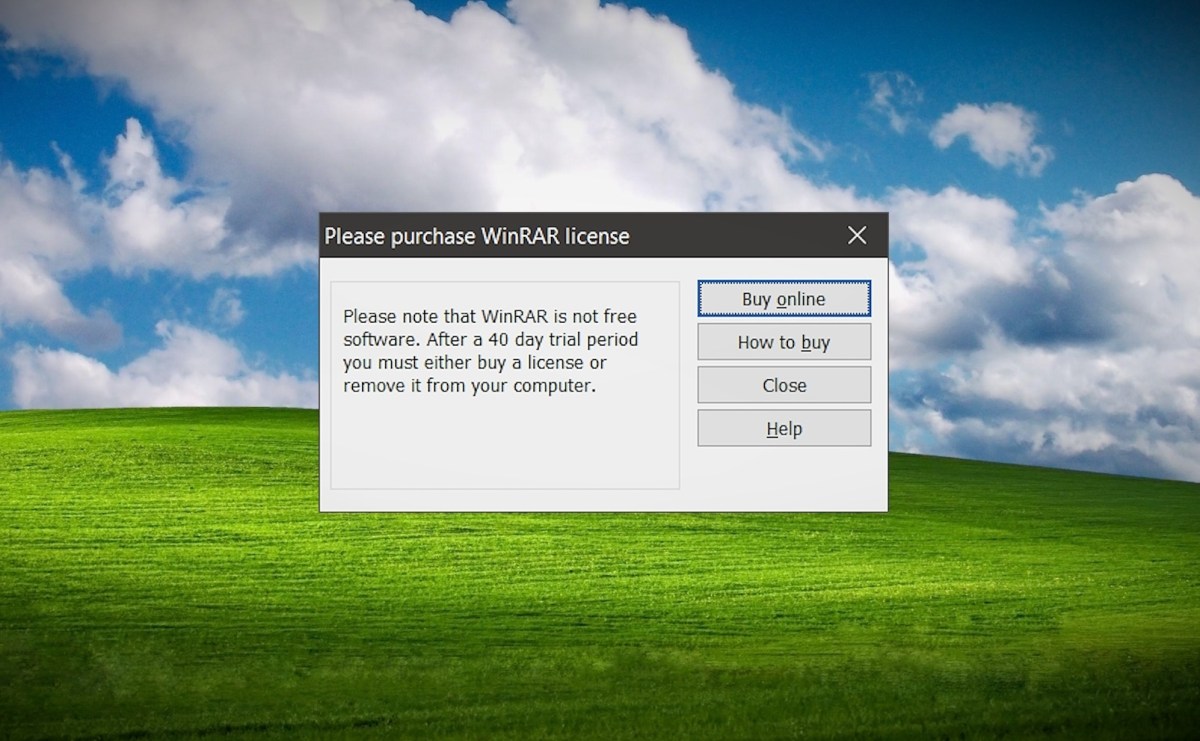
Check Point Research ties Amaranth-Dragon to APT-41, detailing 2025 campaigns across Southeast Asia targeting government and law‑enforcement entities that weaponized the WinRAR CVE-2025-8088 flaw to drop and execute malicious payloads via weaponized archives. The ops use the Amaranth Loader to unload Havoc C2 and later TGAmaranth RAT with a Telegram-based C2 and geo‑restricted infrastructure, plus anti-EDR techniques. The attacks show rapid exploitation of new vulnerabilities and emphasize patching, phishing/weaponized archives, and defense‑in‑depth for regional governments and critical services.