AI-Driven Threats Blur the Line Between Daily Activity and Breach
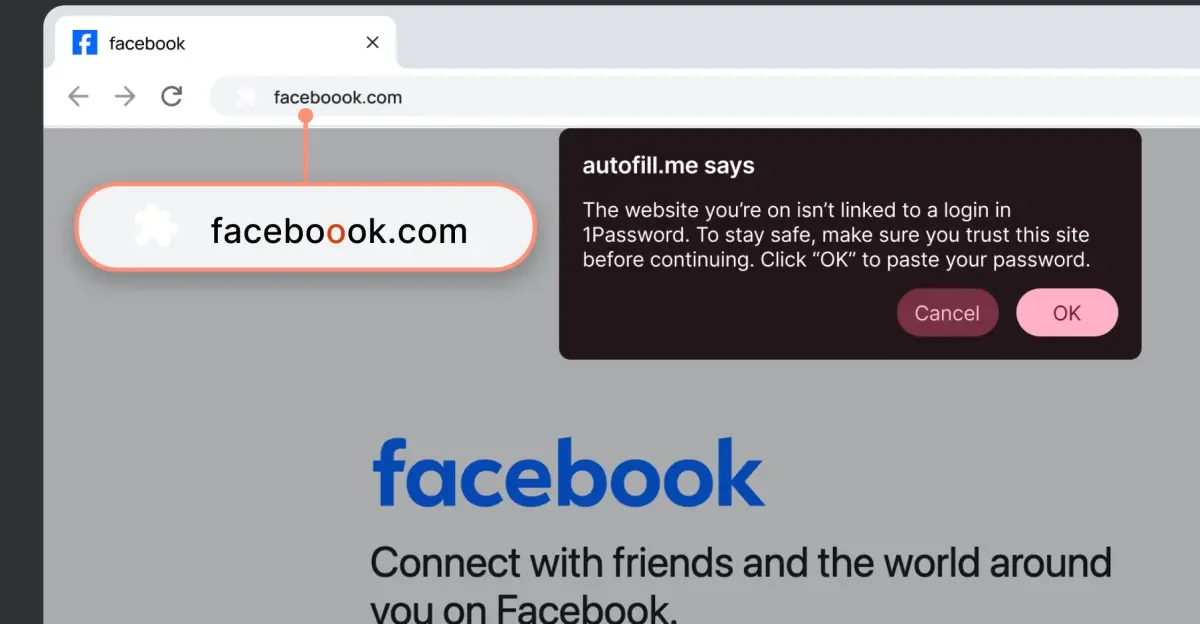
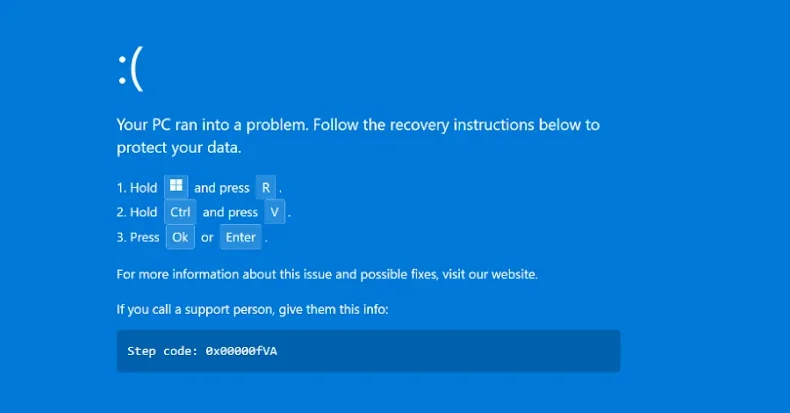
ThreatsDay flags AI-enhanced threats accelerating breaches and blurring into everyday activity: Kali Linux now integrates Claude via MCP for natural-language command execution; campaigns include Bitpanda phishing, four-minute lateral movement, and Mac/WinRAR exploits, aided by ad cloaking, typosquatting, and social engineering, as threat actors fragment post-RAMP and increasingly use AI-driven tactics.