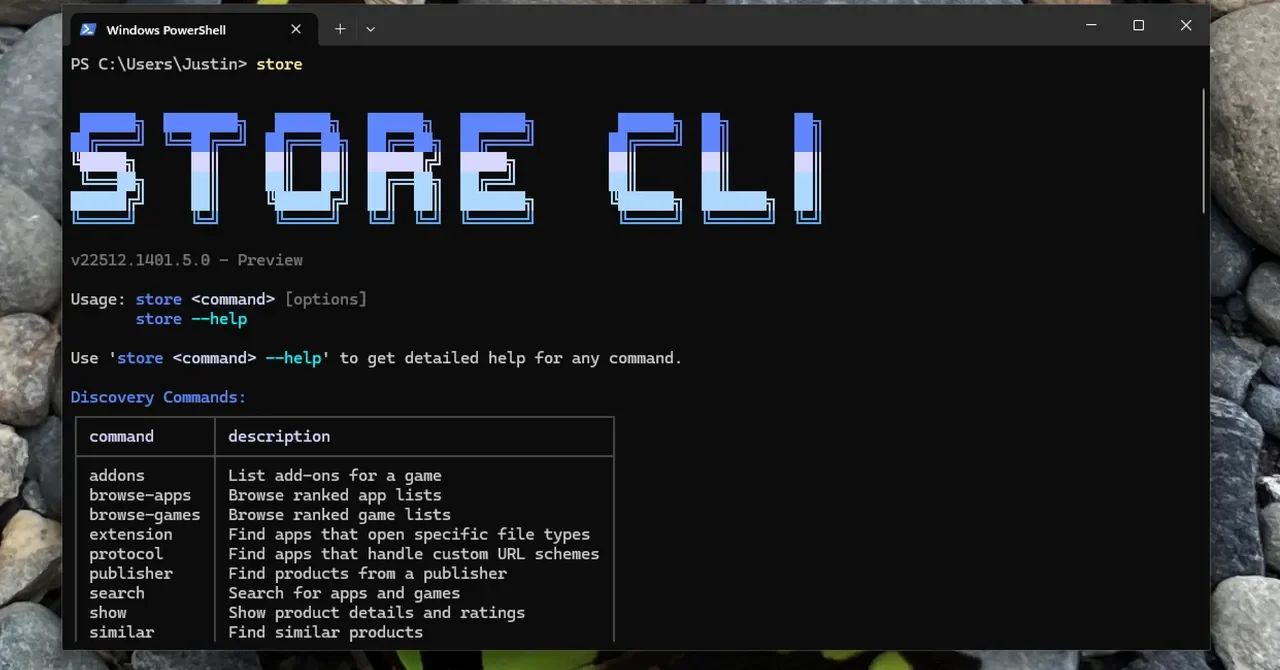
Windows Store Gains a Command-Line Interface for Install and Update
Microsoft introduced a PowerShell-based CLI for the Microsoft Store, enabling search, installation, and updates of Store apps directly from the command line, including bulk updates; however, it only works with Store-listed apps and may not include popular programs like Chrome or Paint.NET.