Months-long Malicious Notepad++ Google Ads Infection Exposed
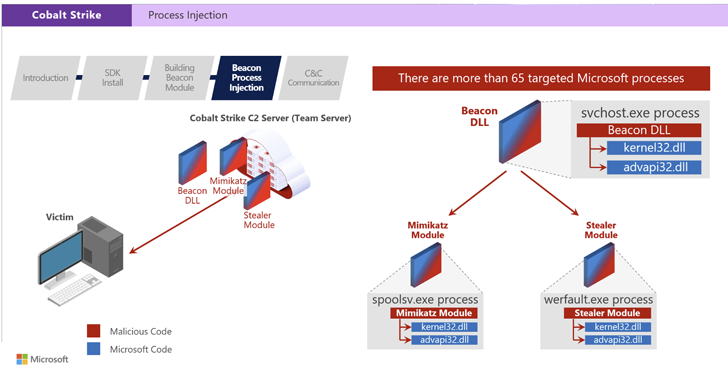
A malvertising campaign targeting users searching for the popular Notepad++ text editor has been active for several months, evading detection. The campaign utilizes Google Ads to promote fake software websites that distribute malware. The final payload is believed to be Cobalt Strike, which often precedes ransomware attacks. The campaign tricks users with misleading titles in Google Search result advertisements, redirecting them to a decoy site or a malicious website that mimics the real Notepad++ site. Victims who meet certain criteria are served an HTA script, likely enabling the attackers to track their infections. To avoid downloading malware, users are advised to skip promoted results on Google Search and verify the official domain of the software they are looking for.