Beware: Android Dropper-as-a-Service Evades Google's Defenses
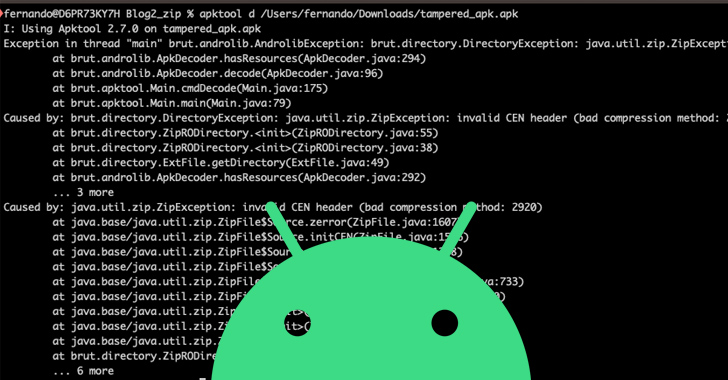
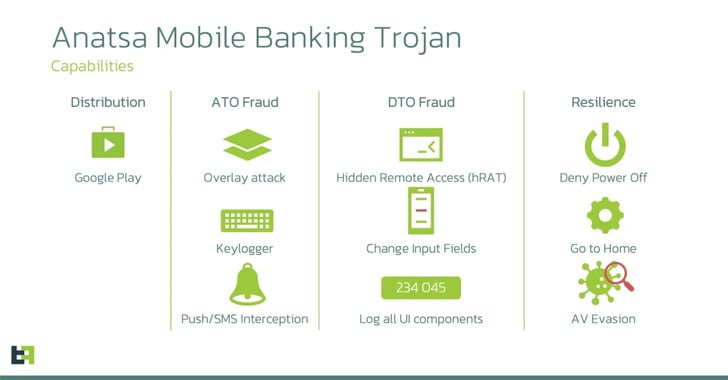
SecuriDropper, a new dropper-as-a-service (DaaS) for Android, has been discovered by cybersecurity researchers. This malware bypasses Google's new security restrictions and delivers the payload. SecuriDropper disguises itself as harmless apps and uses a different Android API to install the payload, mimicking the process used by marketplaces. It bypasses Google's Restricted Settings by requesting permissions to read and write data to external storage, as well as install and delete packages. Android banking trojans like SpyNote and ERMAC have been distributed via SecuriDropper on deceptive websites and third-party platforms. Another similar dropper service called Zombinder has also been observed offering a Restricted Settings bypass.