MacSync Infostealer Lures Mac Users Through ClickFix Social-Engineering Campaigns
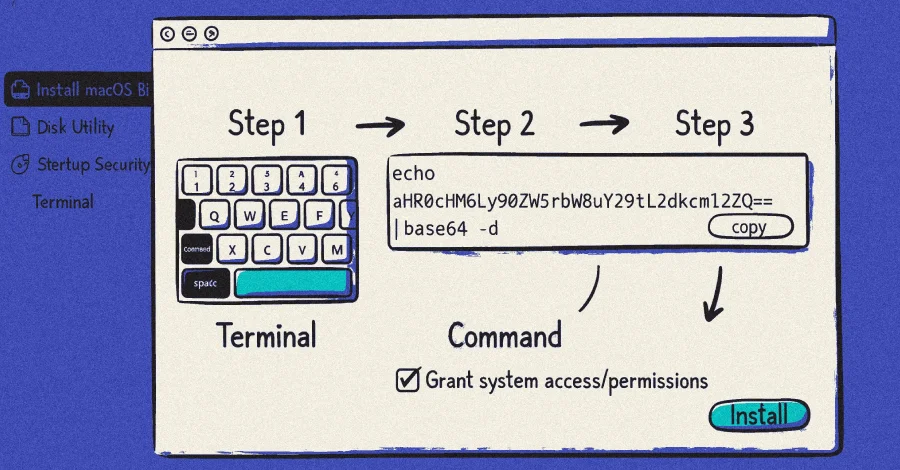
Three ClickFix campaigns have been found delivering the macOS infostealer MacSync by tricking users into pasting Terminal commands to download and run a shell script that fetches the payload and exfiltrates credentials, keychains, and seed phrases. The campaigns (Nov 2025 using OpenAI Atlas bait via Google ads; Dec 2025 via ChatGPT-related pages; Feb 2026 with a new variant) rely on social-engineering lures, malvertising, and trusted platforms to disguise malicious commands and payloads, with in-memory AppleScript execution to evade detection. Defenders are urged to patch hosting platforms (e.g., WordPress), monitor for ClickFix/trojan lures, and maintain zero-trust principles as attackers adapt tactics.
- ClickFix Campaigns Spread MacSync macOS Infostealer via Fake AI Tool Installers The Hacker News
- Evil evolution: ClickFix and macOS infostealers Sophos
- Bad CAPTCHA in the wild tricks Mac users into installing malware through Terminal AppleInsider
- Hackers Use Fake CleanMyMac Site to Deploy SHub Stealer and Hijack Crypto Wallets CybersecurityNews
- MacOS isn’t too much of a safe haven than Windows as infostealers come for Apple computers Yahoo Tech
Reading Insights
1
3
6 min
vs 7 min read
93%
1,399 → 100 words
Want the full story? Read the original article
Read on The Hacker News